Security
How Google is helping you stay safe and secure with your passwords
Can never be too safe

The internet has played a big part in making people’s lives easier and more convenient–from connecting people through emails and social media, online shopping, banking, entertainment and more.
All users have to do is to create accounts for various programs online, which means using their main email addresses and crafting strong passwords to ensure safety.
Nowadays, creating passwords can still be a hassle, that’s why some people resort to easy-to-remember yet vulnerable passwords or keep the same password across all platforms. These may still pose a threat and lead to security risks which can compromise a person’s privacy, their documents, data, and money online.
This is why Google is developing products that are secure to keep people safer online in a way that’s more convenient for them. In celebration of Cybersecurity Awareness Month, here are all the ways Google is making people’s sign-in safer.
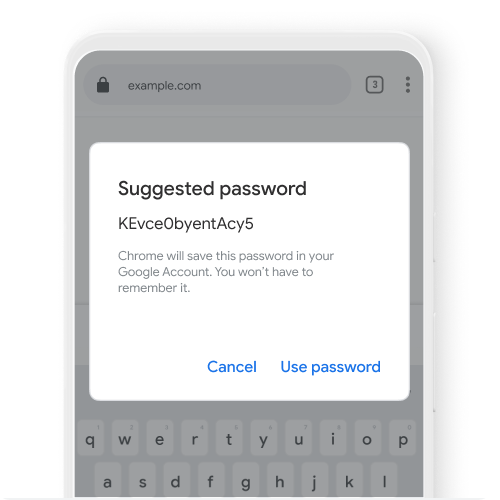
Safe and seamless log-ins with Google’s Password Manager
Every day, Google checks the security of over a billion passwords to protect accounts from being hacked. The tech giant has a Password Manager, which is built directly into Chrome, Android and the Google App.
This uses the latest security technology to keep passwords safe across all the sites and apps. It also makes it easier for people to create and use strong and unique passwords on multiple devices, without the need to remember or repeat each one.
On iOS, people can select Chrome to autofill saved passwords in other apps, too, allowing people to sign-in with just one tap. Chrome is also planning to have iOS adapt the same strong password generation feature, similar to how Autofill with Google works on Android today.
A new feature will also be rolled out in the Google app that allows people to access all of the passwords they’ve saved in Google Password Manager right from the Google app menu.
These enhancements are designed to make your password experience easier and safer across the web, minus the hassle of having to note down or remember different passwords for different accounts like Facebook, Twitter, Instagram, Spotify, Netflix, Canva and more.
Enrolling in Two-Step verification
As attackers still persist in hacking or obtaining illegally what they could, adding a second form of authentication which serves as an extra layer of protection dramatically decreases the chances of getting compromised.
For years, Google has been at the forefront of innovation in two-step verification (2SV), one of the most reliable ways to prevent unauthorized access to accounts and networks.
Two-step verification is strongest when it combines both “something you know”–your password–and “something you have”–like your phone or a security key.
To make 2SV more convenient, a Google prompt will now allow people to simply tap on their mobile devices to prove it’s really them trying to sign in, which guarantees virtually 100% safety provided user’s devices, like their phones, are taken good care of.
Google has also stepped its game when it comes to two-factor authentication, as it has begun automatically configuring people’s accounts into a more secure state.
By the end of 2021, Google plans to auto-enroll an additional 150 million Google accounts in 2SV and require 2 million YouTube creators to turn it on—basically making all Google-related accounts more secure across all its services and products.
At the moment, only Google accounts that have the proper backup mechanisms in place are being auto-enrolled to 2SV. To make sure your account has the right settings in place, take our quick Security Checkup.
Adding security keys into devices
Another innovation Google takes pride in is its security key—a form of authentication that requires people to tap their key during suspicious sign-in attempts.
Say for example, you logged in your GMail into a new device, Google will automatically send a message to your existing device, say a phone, to ask you whether it was you signing in or not.
All you have to do is press either yes or no, or in some cases, Google will ask follow-up questions to make sure nothing gets compromised.
By default, only you can access these prompt-up messages since only you have the control over your phone or your other devices.
Security keys provide the highest degree of sign-in security possible. In fact, Google has partnered with organizations to provide free security keys to over 10,000 people this year who might be vulnerable when it comes to their online security.
Security keys are accessible, as they are built right into Android phones and Google Smart Lock app on Apple devices.
Today, over two billion devices around the world automatically support the strongest, most convenient 2SV technology available.
Towards a safe and secure future
Google recently launched One Tap along with a new family of Identity APIs called Google Identity Services which uses secure tokens, rather than passwords, to sign people into partner websites and apps, like Reddit and Pinterest.
It combines Google’s advanced security with easy sign in to deliver a convenient experience that keeps people safe.
These new services represent the future of authentication and protect against more advanced vulnerabilities like clickjacking, pixel tracking, and other web and app-based threats.
Ultimately, Google wants everyone to have an easy, seamless sign-in experience that includes the best security protections across all of their devices and accounts.

Accessories
Thoughtful gift ideas for modern living: 2025 holiday gift guide
Gift ideas that feel intentional and considered

The best gifts aren’t impulse buys nor extravagant. This year’s holiday gift guide is about giving with intention. Each pick was chosen not as a novelty, but as something that adds value to your loved ones’ lives. They support routines, encourage rest, create shared moments, elevate everyday comforts, and provide peace of mind. These are the kind of gifts that feel considered, personal, and truly meant for the person receiving them.
Peace of mind, wherever the day goes
OrbitKey Travel Sling (3L), US$89.90
This sling is designed for moving through the day feeling organized and secure. Along with its compact, structured layout, it includes RFID-protected pockets that help shield cards and personal information from digital theft. It’s ideal for both commuting and traveling and comes in Black, Stone, and Terracotta.
Statik TireHero Smart Tire Pump, US$69.99
This is the kind of gift that helps people feel prepared rather than reactive. Compact and easy to use, it quickly inflates tires at home or on the road. A small tool that offers real reassurance, it’s especially useful for drivers and cyclists alike.
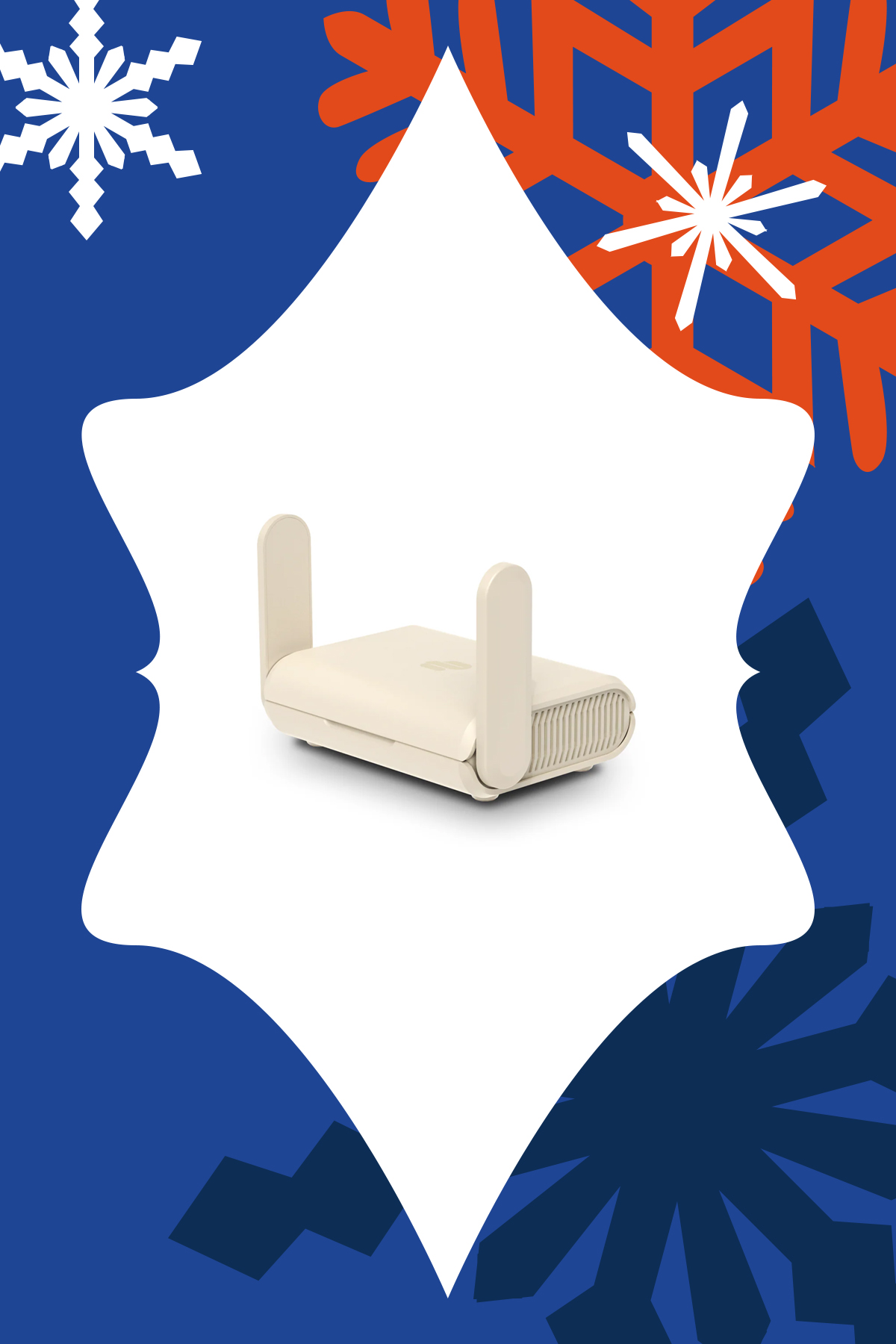
ExpressVPN Aircove Go, US$169.90
This pocket-sized router creates a secure, VPN-protected network anywhere, making public Wi-Fi far safer to use. Ideal for travelers, remote workers, or anyone handling sensitive information on the go. It’s small enough to travel with but powerful enough to protect privacy beyond the home.
OrbitKey Foldable Duffel, US$49
Having an extra bag when you didn’t know you need one can remove a surprising amount of stress and unnecessary expenses. This duffle folds down flat for easy storage, then opens into a 55L bag when packing gets too ambitious and you’re being charged at the airport for your overweight suitcase. It’s reliable, flexible, and quietly reassuring to have on hand.
Thoughtful tech for home and productivity
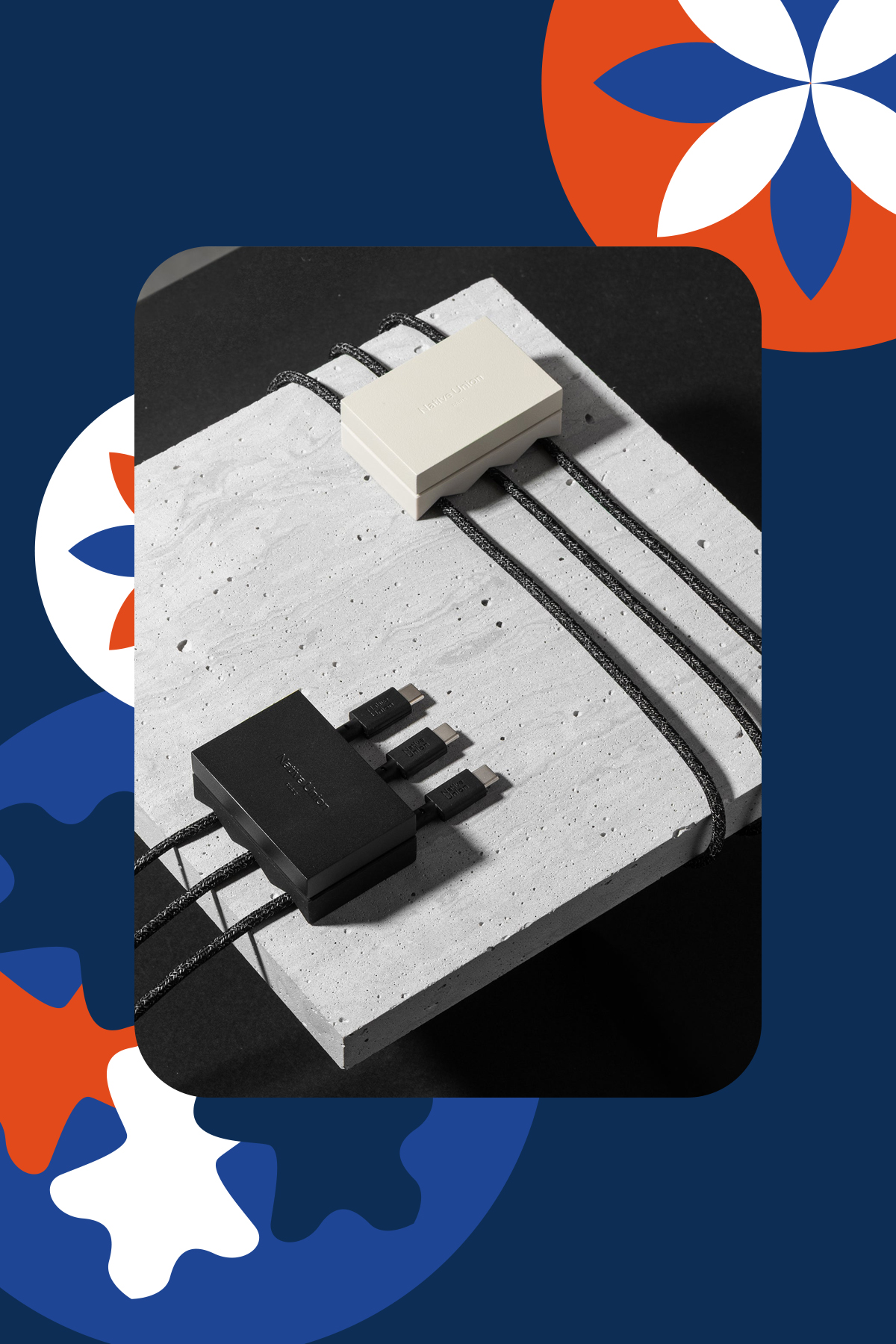
Native Union WEIGHTER, starts at US$19.99
Sometimes the smallest upgrades make the biggest difference. This weighted desk accessory keeps charging cables from slipping out of reach, reducing friction in everyday routines. It’s a subtle but satisfying improvement for someone who works from home or their messy night stand. It comes in Black and Sandstone, and two models: 1 Cable and 3 Cables.
For someone who loves writing by hand but also wants their notes organized digitally, this reusable notebook allows handwritten notes to be stored in the cloud. It’s great for planners, students, even creatives that don’t want clutter. It combines the satisfying tactility of pen and paper and digital convenience.
Built with Qi2 25W, this charger brings calm to the end of the day. With one solid, beautifully weighted base, it charges the iPhone, Apple Watch, and AirPods in one place. It reduces clutter and decision-making, turning charging into a simple ritual.
Lexar SL500 Portable SSD with Magnetic Set, starts at US$105
Extra storage becomes invaluable once someone starts creating, traveling, or documenting more of their life. This portable SSD offers fast, reliable storage with a magnetic sleeve that makes it easy to attach and carry. It’s ideal for backing up photos, videos, and important files without fuss. It’s a practical gift to support that creative in your life and help them stay organized.
Rituals, wellness, and slowing down
Üllo Original Wine Purifier, US$79.99
For someone who enjoys a glass of wine as part of winding down but hates the headaches that come after: Üllo removes sulfites while aerating the wine. It helps enhance the flavor and aroma of wine while being gentler for those sensitive to additives. Add the hand blown Decanter that’s made from ultra transparent lead-free crystal to make any bottle taste fancier.
La Jolie Muse Season of Stories Trio Set, US$60
With artful vessels and clean-burning soy wax, these candles feel as much like decor as they do self-care. The scents are cozy and ideal for winding down or hosting. It’s a gift that invites pause.
LEGO Botanicals, starts at US$14.99
A calming, screen-free build that becomes a beautiful piece of home decor, each set invites someone to slow down and enjoy the process. With flower bouquets, bonsais, and plants to choose from, it’s a satisfying project that brings a sense of completion without the upkeep of real plants. As an added bonus, if you can build it together it turns the gift into a shared memory, so every time they see the finished piece, they’re reminded of the time you spent creating it together.
Small joys, big upgrades
SURI 2.0 Electric Toothbrush, US$135
This device makes an everyday habit feel more intentional. Created with sustainability in mind, it’s a sleek yet practical gift that elevates anyone’s bathroom shelf. It’s got wireless charging and the redesigned travel case powers UV cleaning on the go. It comes in five colors: Winter Fern, Sea Mist, Sunset Bloom, Midnight Black, and Morning Waves.
This portable projector makes it easy to turn any wall into a big screen. You can give the gift of a quiet solo night for someone who needs to decompress from work, or movie nights shared with their loved ones. It’s great for a cozy home setup this winter or the outdoors when the weather starts to get warmer.
Lighting is one of the most overlooked features in any space, but is truly transformative. This smart LED lamp creates soft, customizable ambient light that works indoors or outdoors. It’s perfect for someone who just moved into a new apartment, or that person in your life who cares about mood and intentional design.
Liiton American Peaks Whiskey Decanter Set, US$129
This glassware set transforms drinking into a sensory experience, whether on display or in use. It’s a great conversation piece and makes a nightcap more intentional. Place your glass in the freezer and get chilled and aerated whiskey in just 18 seconds thanks to its proprietary X1 Crystalline Chill Charge System. Made from lead-free crystal, the glassware is sculpted with the majestic U.S. mountain peaks: Mount Whitney, Yosemite, Smoky Mountains, Mount Rainier, and The Rockies.
For growing lives and staying connected
With fewer strings and a simplified design, kids can start playing real songs quickly without feeling overwhelmed. It builds confidence and creativity while introducing musical fundamentals. It’s a gift that supports learning through play.
This gift turns fleeting moments into tangible memories. With a few taps, photos on your phone become physical prints that can be shared, saved, and displayed. In an age where taking photos has never been easier, having physical prints encourages reminiscing without increasing screen time. It’s a wonderful gift for families and friends who love documenting life.
Arzopa Digital Photo Frame, starts at US$99.99
Bring warmth to someone’s home without requiring technical effort. This photo frame is great for that loved one who’s moved far away. Photos can be updated remotely, making it easy to feel closer despite the distance. It comes in two sizes: 10″ and 14″, both with a champagne colored bezel.
Apps
Don’t get tricked: Spot these financial monsters before they get you
Ghosts are harmless compared to these real-life threats that prey on your hard-earned money.

The spooky season has arrived, but not all monsters wear masks. Some hide behind fake links and shady offers designed to trick you into giving up your hard-earned money.
These are the real-life financial monsters: fraudsters, impersonators, and manipulators who turn everyday moments into horror stories.
According to the Cybercrime Investigation and Coordinating Center, 32% of Filipinos have fallen victim to digital fraud in the past year. And while it’s tempting to think you’d never fall for one, scammers are getting smarter and more creative.
Here’s what to watch out for:
Suspicious links and emails.
Those random texts and emails saying “there’s a problem with your account” or “you’ve won a prize”? They’re classic traps.
Scammers disguise themselves as legitimate companies to steal your information or access your accounts. Always double-check the sender’s address. If it looks off, don’t click.
Grammar gone wrong.
If a message is full of weird typos, awkward phrasing, or off punctuation, that’s a red flag.
Reputable companies review every message they send. When in doubt, don’t reply. Report it to authorities like the PNP Anti-Cybercrime Group or the NBI.
Urgent and emotional messages.
Scammers love to pressure you. They’ll make you feel scared or guilty to get you to act fast.
Real companies won’t threaten or rush you into sharing personal info. Take a breath, hang up, and reach out to the official hotline to verify.
Deals that sound too good to be true.
If someone promises instant money or massive discounts, run. These scams often demand “processing fees” or personal info before disappearing. No legitimate prize will ever require payment upfront.
Behind every scam is a story of someone who deserved better. Sometimes, what started as a simple loan application can turn into a nightmare if a rogue online lender decides to harass someone over payments they didn’t even fully receive.
It’s a familiar story for many Filipinos who’ve been preyed on by unregistered or unethical financial services.
Thankfully, more responsible lenders and financial platforms today (Tala, for example) are working to raise awareness and fight back against these threats.
Some even use advanced systems to flag suspicious behavior, partner with authorities for investigations, and educate communities through financial literacy programs.
At the end of the day, awareness is your strongest defense. So this Halloween, stay sharp because protecting your peace (and your money) will always be the sweetest treat.
News
McAfee rolls out an easy way to detect scam texts and emails
Plus, they have a much lighter app.
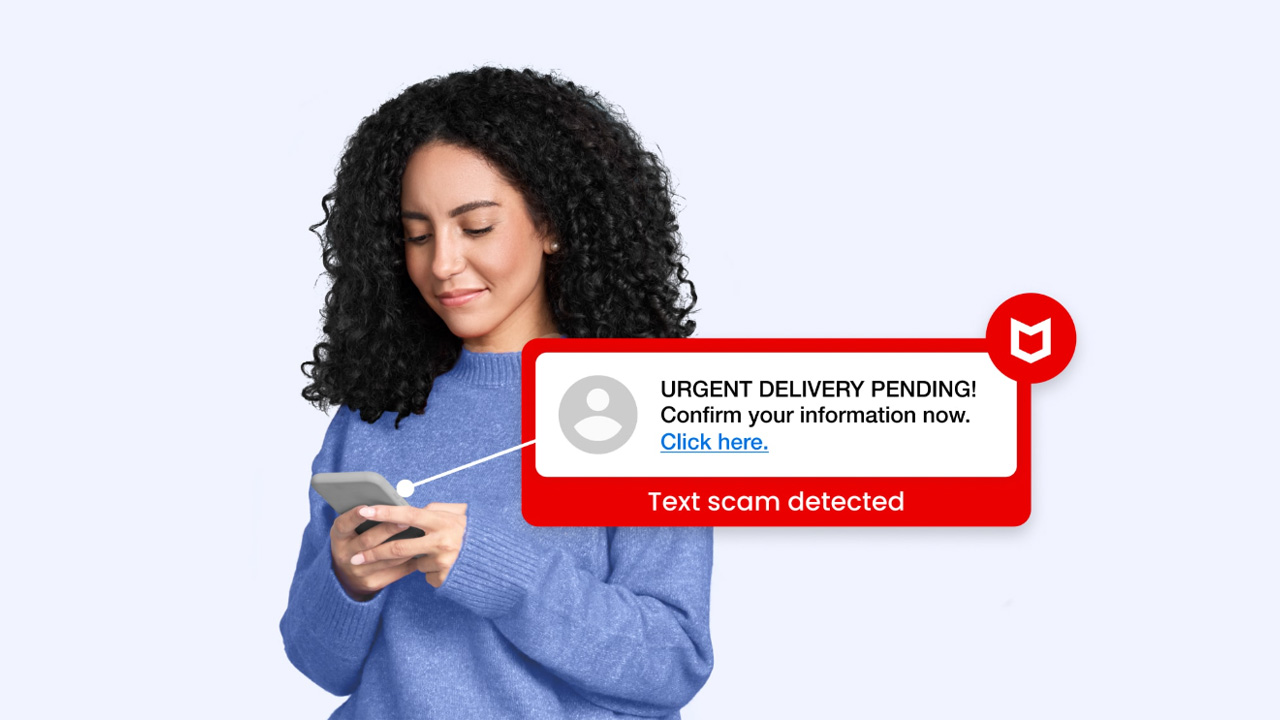
Scammers are getting more brazen these days. Instead of going through the same scripts, malicious actors are now going for more robust schemes to impersonate official accounts. It’s impossible to go through a single week without a warning to never trust suspicious senders or links. To fight the latest wave of malicious parties, McAfee is launching new features to more easily find and eliminate potential threats.
As reported by McAfee, 88 percent of Americans have encountered a scam in the past year. The average person sees about 14 scams on a single day. And it’s not just exclusive to the United States. Everyone all over the world is falling prey to scammers more accurately presenting themselves as legitimate accounts.
Introducing the McAfee scam detector
To fight this, McAfee now has a scam detector. Using the power of AI, the antimalware service can scan both text messages and emails for potential scams. It can also block suspicious links for you.
Now, because the software now uses AI, it can also use the same technology to more easily present why it found a threat. In the past, McAfee just showed users the errant file and called it a day. Now, the software offers readable explanations as to why the detected file might be a threat. It’s the perfect tool for those who aren’t savvy with computers.
Additionally, the same feature can analyze videos to see if they’re deepfakes. Of course, not every deepfake is a scam. But knowing if a video might be generated is a crucial skill these days.
A much lighter app
Despite adding a significant feature against modern scams, McAfee has somehow made its software lighter for modern PCs. According to a performance test from AV-Comparatives, McAfee ranks the lightest compared to other titans in the segment including Avast, AVG, and Kaspersky. Basically, using McAfee takes the least toll on your PC.
More interestingly, this comparison includes Microsoft Defender. There used to be a time when experts said that Microsoft’s built-in antivirus software was much better than most paid services. Now, it seems McAfee is fighting back against the claim by offering a much lighter service that can work in the background without interrupting whatever you’re doing.
Available on all plans
Importantly, McAfee’s new scam detector is available on all plans. It’s also available for mobile, tablet, and PC use.
However, it isn’t available for all territories yet. McAfee is still working to get the feature implemented in other languages.
-

 Gaming2 weeks ago
Gaming2 weeks agoLevel Infinite launches Gangstar Mirage City exclusively in PH
-

 Singapore1 week ago
Singapore1 week agovivo Y Series launches in Singapore with bigger battery, durability upgrades
-

 Reviews2 weeks ago
Reviews2 weeks ago5 games with the nubia Neo 5 GT 5G
-

 Automotive2 weeks ago
Automotive2 weeks agoThe VinFast VF6 is perfect for urban travelers
-

 Gaming2 weeks ago
Gaming2 weeks agoThe Blood of Dawnwalker launches September 3
-

 Gaming2 weeks ago
Gaming2 weeks agoThe Steam Controller is coming out on May 4
-

 Gaming2 weeks ago
Gaming2 weeks agoFinal Fantasy VII Rebirth demo out now on Switch 2 and Xbox
-

 Gaming1 week ago
Gaming1 week agoPRAGMATA is not for the faint of heart